The advent of the Internet of Things (IoT) offers potential for more efficient control of an ever smarter world. But IoT is expanding so rapidly that it poses a risk to IT security. Wallenberg Academy Fellow Panagiotis “Panos” Papadimitratos aims to prevent critical societal functions being taken over by hackers.
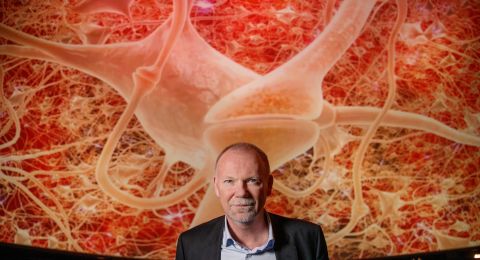
Panagiotis Papadimitratos
Professor of Networked Systems Security
Wallenberg Academy Fellow, prolongation grant 2018
Institution:
KTH Royal Institute of Technology
Research field:
Security and privacy for networked systems
More and more devices around us are connected to the internet. They include everything from smart speakers, heat pumps and street lighting to automobiles and buses. There is a growing need for interconnected devices in our daily lives. The Internet of Things is expanding far faster than many people realize.
“Emerging smart environments, whether private or run by the state, may be highly vulnerable to hackers. My vision is that we can prevent the transition to a smart society from becoming a dystopian future,” says Papadimitratos.
New ways of improving security
In his view, current security solutions are not designed to handle the complexity and scale of the IoT. Yet, IoT devices and applications are being rolled out in the market at an increasing pace.
“These days a multitude of technologies are developed and launched without those behind them considering carefully how they could be attacked. The very nature of IoT makes it necessary to develop new ways of strengthening security,” he says.
Nor are new solutions fully tested in the highly automated and complex environments in which they are to be used. It is important to expect that IoT devices can be compromised, controlled or even cloned by adversaries.
Papadimitratos has an essentially holistic approach to his research. He moves from theories and design in pure research to real-world testing environments. If a new protocol or security system is to have an impact on IoT, it is not enough for it merely to improve security. It must not be too costly to implement or negatively impact performance, system safety or user privacy.
“It is vital to understand this multidimensional challenge, with its trade-offs. With solid methodology, thoroughly analyzed, efficient solutions, proof-of-concept implementations and demonstrators. So that research results are adopted and we deploy trustworthy IoT systems and applications.”
Papadimitratos’ research has attracted the attention of the Internet Research Task Force (IRTF), which awarded him the Applied Networking Research Prize (ANRP) in 2018. The prize recognizes research and development that is likely to become part of the next generation internet. His research has influenced standards and the understanding of the industry, e.g., on security and privacy for connected vehicles.
Raising the security bar for self-driving vehicles
Connected and self-driving vehicles of the future set the bar for IoT security standards. When these vehicles are traveling our roads, they need to be able to communicate with each other and their surroundings. To navigate, they also need information from route planners, map services and GPS satellites. Communication must take place as fast as possible to avoid accidents.
But how can the identity of different vehicles, sensors in the surroundings, and the global positioning system be assured? All information must be reliable so that the vehicles can make the right decisions. If any part of the system is hacked, the other parts of it need to be protected on-the-fly, and attacking or faulty devices promptly removed from the system.
The same goes for sensors in a building or factory, which can often also be manipulated physically, or spoofed global navigation systems affecting location-based applications, or mobile crowd-sensed measurements ‘poisoned’ by malicious or selfish participants. Ways are therefore also needed to determine whether the data being communicated appear reasonable and reliable.
“A line of defense is needed that is capable of repelling cyber-attacks, managing trust across the system, and determining whether the data you receive are reliable. All this must be achieved on an agreed scale and constructed so as to create a modern and manageable security system,” Papadimitratos explains.
Adding new security solutions to an existing system can itself be a risk. If it renders the system vulnerable to overload from a deluge of data, the security solution itself becomes a security problem.
Nor must the security system leak information that you do not want to share with others. This is something that Papadimitratos thinks is far too common these days.
“But we’re becoming increasingly aware of this as users, and can choose to avoid certain products and services because they spread too much information about us,” he says.
Yet there may be situations, as in a terrorist attack, where a public agency needs access to more information than is normally shared.
“The grant I’ve received from Knut and Alice Wallenberg Foundation gives me an opportunity to go further in my research, and also a platform for spreading the results. So, the funding is a catalyst for the development of a trustworthy IoT.”
The aim of Papadimitratos’ research is to develop mechanisms and building blocks capable of meeting all these security and privacy challenges. He hopes to facilitate the spread of solutions by building broadly applicable blocks for security and privacy protection.
“The greatest difficulty is the wide diversity of the Internet of Things. To create secure and reliable environments, we first have to gain a thorough understanding of all the technologies involved. If we develop key enablers for security and privacy, solutions relevant to many future systems and applications, then hopefully they will have a greater impact.”
Text Magnus Trogen Pahlén
Translation Maxwell Arding
Photo Magnus Bergström