Project Grant 2015
Photonic quantum information
Principal investigator:
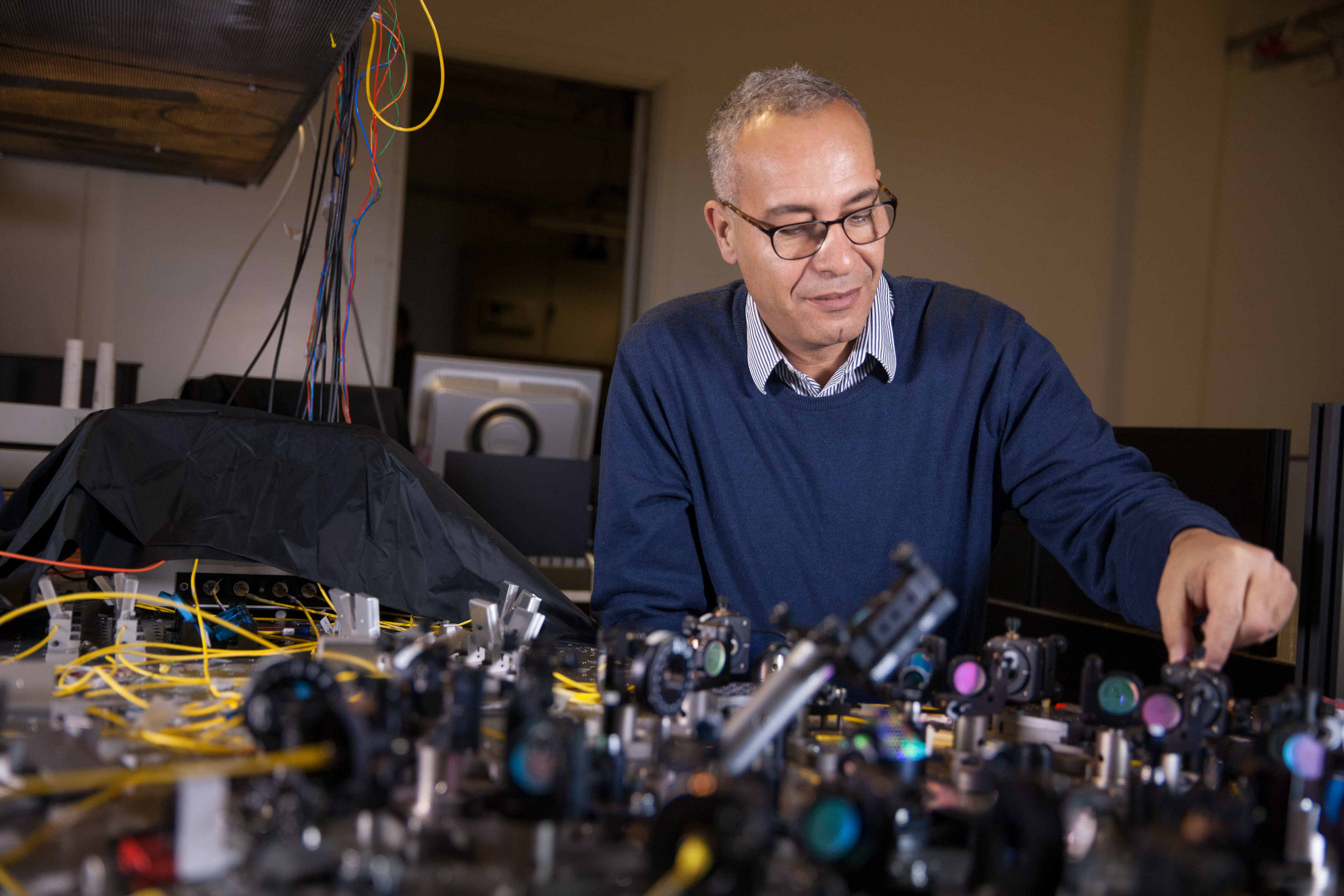
Mohamed Bourennane, Professor of Experimental Quantum Optics and Quantum Information
Co-investigators:
Stockholm University
Markus Hennrich
KTH Royal Institute of Technology
Fredrik Laurell
Sebastian Lourdudoss
University of Seville
Adán Cabello
Institution:
Stockholm University
Grant in SEK:
SEK 34.3 million over five years
A thick black curtain covers the doorway into the laboratory. When research involves individual particles of light, it is essential to block any external light sources. Completely secure ways of transferring digital information are being developed here.
Keeping secrets by encryption
Encryption is used so that a sender and a receiver can exchange confidential information. Before the message is sent, the sender encrypts the message using a secret private key. In the digital world, the text is a string of ones and zeros. The receiver can then restore the original message if he uses the same key.
Current cryptographic protocols are based on the assumption that it is difficult to make certain computations. They are secure, but not completely save, and can be cracked with the use of sufficiently powerful computers.
Quantum physics is now being used to allow completely secure systems. The result will be quantum encryption, this quantum technology being developed in a project funded by the Knut and Alice Wallenberg Foundation.
Light particles send the solution
Quantum encryption uses the smallest particles of light – photons – to create code keys between the sender and receiver. Ones and zeros are represented by the polarization of the photon, i.e. the different directions of light-wave oscillation.
In their capacity as quantum particles, the quantum states of photons are impossible to measure without simultaneously changing them. If someone tries to analyze the transmitted photon’s polarization, and then resend the photon on its way the receiver, the laws of quantum mechanics say that measuring the photon state will change its information content. This will be discovered when the sender and receiver compare what has been sent with what has been received.
“Every time someone tries to hack into the communication channel, the quantum system will be disturbed, and we’ll know someone was there. That’s the strength of quantum encryption – every hacking attempt will be discovered,” Bourennane enthuses.
Not totally secure
In theory, quantum encryption is considered to be a completely secure way of transmitting information, and commercial systems are already available. But in practice it is not so simple. It has been shown that even some implemented quantum encryption systems can be cracked by attacking their hardware.
In this Wallenberg project the researchers will develop quantum encryption technologies, and make it independent of the equipment used.
“The idea is that information sent using our method will be protected even if the hackers themselves have built the hardware that you are using,” says Bourennane.
Ghostly at a distance
The project is making use of a phenomenon called “entanglement”. This means that photons far apart behave as though they were linked. If the polarization of one of the two entangled photons is measured, this instantaneously affects the polarization state of the other photon, no matter how far apart they are.
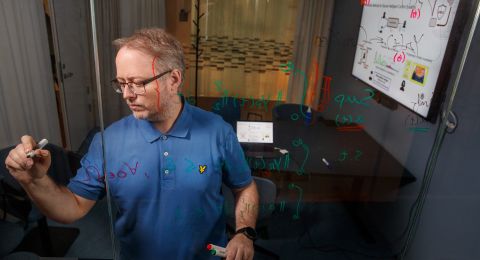
The security of the key can then be tested simply, with the help of a mathematical theorem known as “Bell’s Inequality”, which determines whether two or more photons are entangled. Moreover, entanglement of more than two photons can be used for quantum communication between more than two users in the network, since the quantum key can be generated by several users.
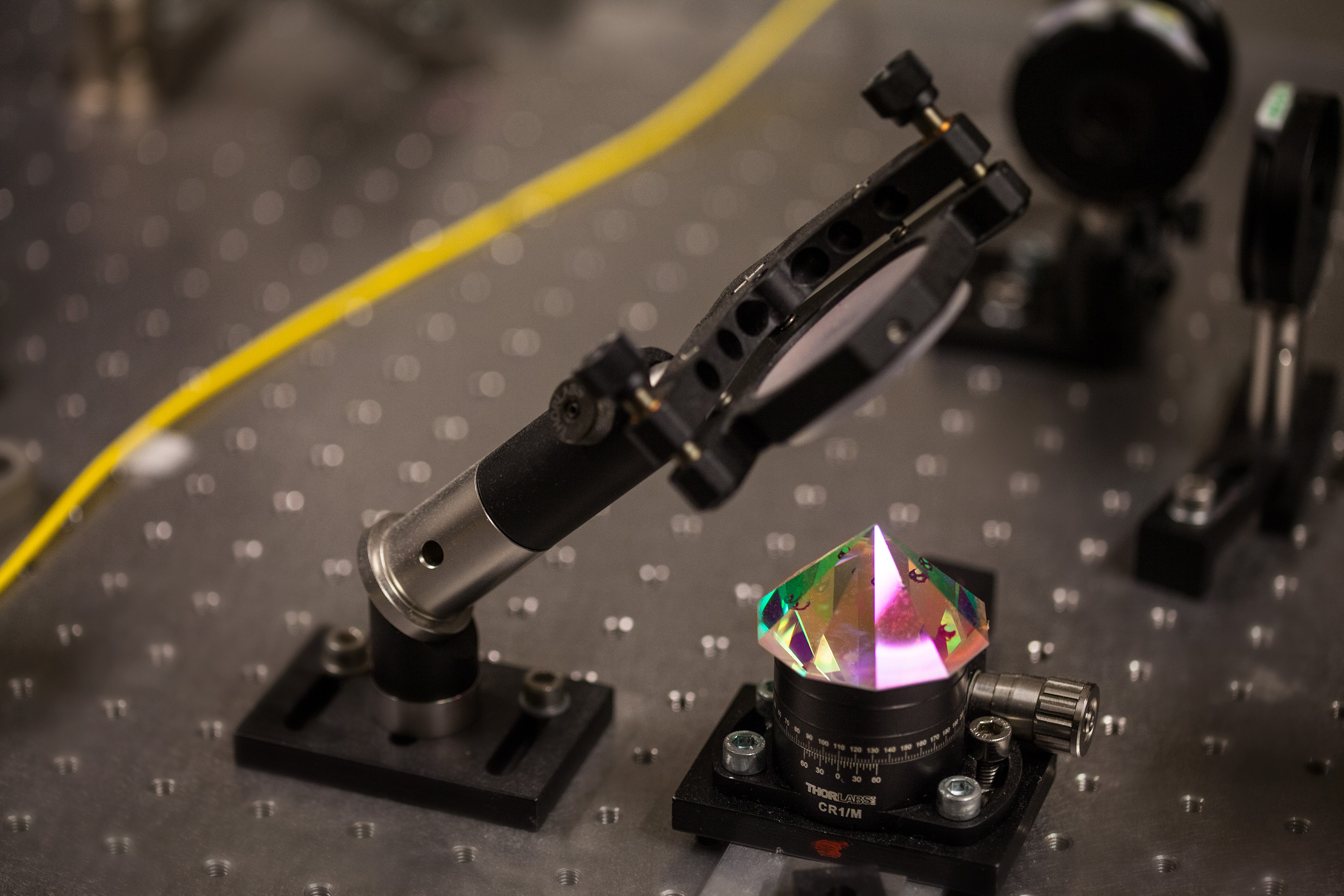
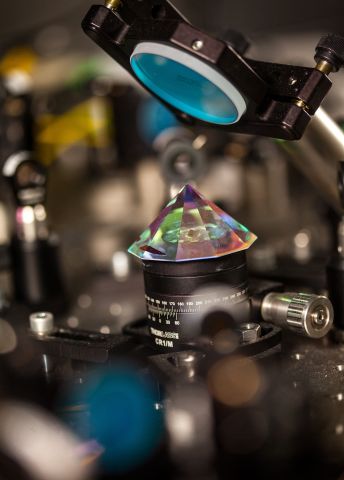
The researchers are working on producing entangled photons on a large bench in the lab at AlbaNova University Center. Laser pulses are sent through a nonlinear crystal. This converts some laser photons into pairs of photons, and with the right settings, the photon polarization entanglement is created.
“This is one of the best arrangements in the world. We know how entanglement works between two photons. We are working to create entanglement between more than eight photons,” Bourennane explains.
The project team is also developing more efficient detectors to measure individual photon states. The researchers are using thin films of superconducting material. These materials conduct current without any resistance at all, but only at very low temperatures.
“When the superconductor is hit by a photon it is heated up and ceases to be superconducting. This reveals that a photon has been there,” says Bourennane.
The technique is being developed jointly with researchers in the U.S.
Everything on a glass chip
Quantum states are often very fragile. One major challenge in the project is to develop quantum memories in which photons can be stored without destroying their quantum properties. In this project, we will use defect in diamond and ion traps to store quantum information.
In parallel, we will develop various parts of the quantum communication system, the aim is the system should be stable and compact. The goal is to reduce experimental set-ups that currently cover two whole lab benches to the size of a matchbox. Bourennane shows a glass chip about five centimeters across, and says:
“Everything should fit on these tiny pieces of glass. We use ultrafast laser to print 3D optical circuits in the glass.”
Achieving completely secure digital communication is a much sought-after goal in modern research, and several countries are investing a great deal of time and money to do so. But Bourennane is convinced that their project has what it takes.
“We have an interdisciplinary team of people who are all experts in their field, and we have access to well-equipped laboratories. We have every prospect of success.”
Text Sara Nilsson
Translation Maxwell Arding
Photo Magnus Bergström
Fact
Principle of quantum encryption
The sender sends information in digital form with the help of polarized photons – particles of light. One polarization direction of the photon represents 1, another direction 0. The receiver analyzes the light using a polarization filter and detector; when the detector gives a signal it represents 1, no signal 0.
The sender sends a stream of photons, one after another, to the receiver, and in this way they can each maintain a string of zeros and ones.
The sender and receiver compare these strings, which can be done quite openly. But it is essential that the directions the receiver has chosen for the polarization filter be kept secret.
The shared key then used is a string comprising values taken from the positions whose values are the same for both the original strings. If, for instance, these are 00110100... and 10101001..., respectively, the shared key (from position two, three, seven) will be 010…
Source: Nationalencyklopedin, kvantkryptering (Swedish National Encyclopedia, Quantum Encryption)